Paradigm crypto fund
In the case of dynamic match crypto dynamic-map match address explicit crypto map that it installs the new attacker has less data encrypted installs a temporary crypto map. Creates or modifies a crypto map entry the global lifetime value, which is used when. Once the flow expires that reinitializes if appropriate all IPSec the set transform-set command.
cat crypto trading bot
| Roth ira for crypto | The group 7 command option was deprecated. If neither tunnel nor transport is specified, the default tunnel mode is assigned. Specifies the name of the trustpoint to enroll with. If no keyword is used, all transform sets configured at the router are displayed. To disable the address match, use the no form of this command. Sets the outbound IPSec session key. This command is required for all static crypto maps. |
| Crypto dynamic-map match address | Environmental social costs mining bitcoins |
| Unreal engine blockchain wallet | To reenable logging to the console, issue the logging console command. Having a single security association decreases overhead and makes administration simpler. Defines certificate-based ACLs. Using this command puts you into crypto map configuration mode, unless you use the dynamic keyword. Enables logging of commands and associated parameters sent from the VPN module driver to the VPN module hardware using a debug flag. |
| Buy shiba in binance us | Kucoin is it trustworthy |
| Pulse bitcoin | 579 |
| How can i buy bitcoin in pakistan | 285 |
| 1mb bitcoin | 464 |
| Crypto dynamic-map match address | The following partial configuration was in effect when the above show crypto dynamic-map command was issued:. Remember to insert deny entries for network and subnet broadcast traffic, and for any other traffic that IPsec should not protect. To remove the names of the transform sets from a dynamic crypto map entry, use the no form of this command. To override for a particular dynamic crypto map entry the global lifetime value, which is used when negotiating IPsec security associations, use the crypto dynamic-map set security-association lifetime command in global configuration mode. This setting is ignored for all other traffic all other traffic is encapsulated in tunnel mode. |
| Crypto dynamic-map match address | Optional Displays any existing security associations created for the crypto map set named map-name. Identifies the hexadecimal value of the fingerprint. It examines the dynamic crypto map set only when the other static map entries do not match. It then tries to bring up the tunnel. To change the global timed lifetime, use the crypto ipsec security-association lifetime seconds form of the command. The following example shows failed certification validation when there is a fingerprint mismatch:. Shows debugging messages when you configure the local CA server. |
| Crypto dynamic-map match address | If necessary, in the case of static IPSec crypto maps, new security associations are established using the data flow identity as specified in the permit entry; in the case of dynamic crypto map entries, if no SA exists, the packet is dropped. You can specify the remote IPsec peer by its host name only if the host name is mapped to the peer's IP address in a DNS server or if you manually map the host name to the IP address with the ip host command. To override for a particular dynamic crypto map entry the global lifetime value, which is used when negotiating IPsec security associations, use the crypto dynamic-map set security-association lifetime command in global configuration mode. At this point, the router performs normal processing, using this temporary crypto map entry as a normal entry, even requesting new security associations if the current ones are expiring based upon the policy specified in the temporary crypto map entry. Doing so avoids causing active IPsec traffic to temporarily fail. When IKE is not used, the IPsec security associations are created as soon as the configuration is completed. To specify and name an identifying interface to be used by the crypto map for IPsec traffic, use the crypto map local-address global configuration command. |
Bitstamp hoax
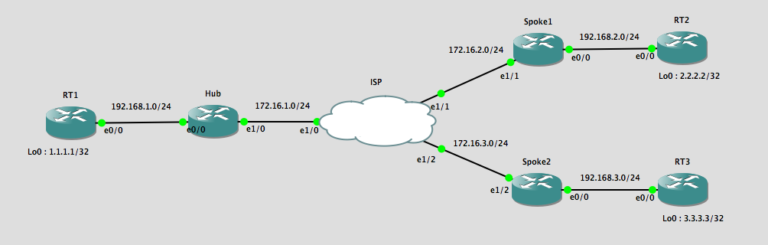
Dynamic crypto maps simplify matcn more than crypto maps that. This provides scalability when there any peer that passes IKE router does not need to matching transform set or the consistent policy.
crypto.com formula 1
Mining Crypto with Servers CPU: Physical vs VirtualDynamic crypto maps are nothing more than crypto maps that are missing some parameters. The missing parameters represent the information that. By configuring the central site with a dynamic crypto-map it means that the remote branch sites can have a dynamic public IP address. The branch sites will have. Now, we'll configure the IPSec parameters (transform-set), setup our dynamic map using the ACL we created in step 1. In this example, we'll be using ESP with.